Janine Jackson interviewed Muslim Advocates’ Sumayyah Waheed about CNN‘s John Miller for the September 16, 2022, episode of CounterSpin. This is a lightly edited transcript.
Janine Jackson: In March of this year, John Miller—then deputy commissioner of intelligence and counter-terrorism for the New York Police Department—told a New York City Council meeting that “there is no evidence” that the NYPD surveilled Muslim communities in the wake of September 11, 2001—”based,” he said, “on every objective study that’s been done.”
NPR (4/15/14)
At that point, media had extensively documented the unconstitutional discrimination of the NYPD’s so-called “Demographics Unit,” including installing police cameras outside mosques, and reporting store owners who had visible Qurans or religious calendars. And the NYPD had agreed to disband the unit in the face of multiple federal lawsuits.
In September, CNN hired John Miller as “chief law enforcement and intelligence analyst,” part of changes attached to CNN‘s absorption by Warner Brothers Discovery, whose most powerful shareholder is libertarian billionaire John Malone, who has stated that he would like CNN to feature more “actual journalism,” citing, as an example, Fox News.
Forget what it portends for CNN. The Miller hire is a message to Muslim communities about who it’s OK to harm under official sanction, and how eagerly some will strive to deny and erase that harm and its ongoing effects.
We’re joined now by Sumayyah Waheed, senior policy council at Muslim Advocates. She joins us now by phone. Welcome to CounterSpin, Sumayyah Waheed.
Sumayyah Waheed: Thank you so much for having me.

CNN‘s John Miller
JJ: I want to read just a little bit more context for the statement that John Miller made to New York City Council member Shahana Hanif, when she asked for transparency and an official apology for the NYPD surveillance and harassment of Muslims.
Just before he said there’s no evidence, Miller said:
Perception allowed to linger long enough becomes reality. I know from my own conversation with Muslim members of the community, and Muslim community leaders, that there are people…who will believe forever…[that] there were spies in their mosques who were trying to entrap people.
It seems important to acknowledge that this isn’t just lying. This is gaslighting, right?
SW: Yeah. And it’s lying under oath. He was providing testimony under oath to the City Council.
It’s important to note he had choices in terms of how to respond to this, the request for an apology. He could have flatly refused it. He could have defended the NYPD’s program. I wouldn’t agree with that, either, but he could have done that.
Instead, he chose to lie about something that’s well-documented. And as you said, specifically something that harms a marginalized community, the Muslims in the New York area, whose harms that they suffered from this massive surveillance echo through today.

Pulitzer Prizes (2012)
And this was not that long ago. This program started in the aftermath of 9/11, so about 20-plus years ago, and then the AP reported on it in, I think, 2012. They won a Pulitzer Prize for their reporting on it.
And they reported with a treasure trove of documents, internal documents from the NYPD, some of which our organization utilized in our lawsuit against the NYPD for their spying. And a federal appeals court explicitly said that our client’s allegations were plausible, that the NYPD ran a surveillance program with a facially discriminatory classification.
So he chose to lie about something that’s well-documented. He chose to basically spit in the face of Muslim communities who were harmed by this program. And he has basically been rewarded for it, by being hired by a major news outlet with a position that, I don’t even know how much he’s going to be compensated, but he’s now got a national platform to further spread lies.
JJ: It’s incredible, and I just want to draw you out on one piece, which is that folks, even critically thinking folks, will have heard, yes, this was a program that happened, but it was ended, despite what Miller, in his brain, which we don’t want to explore, believes. The program ended, and so therefore maybe things are better.
Could I just ask you a little bit about the harms from something like this surveillance program, which is—cameras outside of mosques, interrogating people in stores, you know? The harms don’t disappear when the program is officially ended.
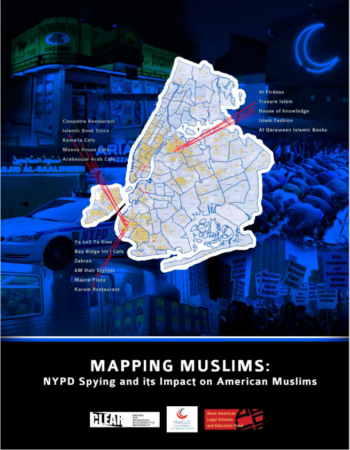
CLEAR et al. (2013)
SW: Not at all. So first of all, just from our lawsuit—and our lawsuit was specifically for New Jersey Muslims who were affected by this, and there were other lawsuits for the New York Muslims, and there were Muslims outside of the New York and New Jersey area who were affected by this. But just from our lawsuit, we knew that the NYPD spied on at least 20 mosques, 14 restaurants, 11 retail stores, two grade schools and two Muslim student associations in New Jersey.
So every aspect of Muslims’ lives was being surveilled, and the community finding out about this pervasive surveillance, that’s not something that you can just dismiss. The community basically was traumatized by this.
And the result—there’s a Mapping Muslims report that actually goes into all the effects, some of the impacts on the Muslim community from this notorious program of surveillance. And they found that Muslims suppressed themselves, in terms of their religious expression, their speech and political associations.
It sowed suspicion within the community, because people found out, you know, the person sitting next to me at the mosque was an informant. How can I go to the mosque and trust everyone there? Maybe I won’t go.
Of course, it severed trust with law enforcement, and then contributed to a pervasive fear and unwillingness to publicly engage.
So that you can’t just flip a switch on. If the NYPD actually wanted to address those harms, that would be a really long road to repair.
And by having John Miller in his position, and not actually censuring him or firing him for those comments, the NYPD signaled the opposite, right, that they’re going to back somebody who doesn’t care to address the harms of the department.
And then, of course, now he’s being further validated by a national news media company.

FAIR.org (6/21/17)
JJ: And Miller does Big Lie—a term, by the way, that is now reportedly forbidden at CNN with reference to Trump’s stolen election.
But in 2017, as Josmar Trujillo wrote for FAIR.org, Miller was on a local radio station, WNYM, saying that
activists have in their mind this idea that police departments and cities like New York run massive surveillance programs, targeting innocent civilians for no reason. Now, that’s nutty. I mean, why would we do that? How could we do that? And how would it make sense?
Again, this is beyond misinformation to disinformation. And it’s very clear that this is his jam, you know? And so CNN has to want him for that, and not despite that. It just, it’s breaking my brain.
SW: Yes, because news networks should be helping us sort fact from fiction, not further destroying the line. Otherwise they’re nothing better than propaganda machines.
And this is not just propaganda. This is specifically erasing the experiences of marginalized people —and to elevate law enforcement above any criticism, much less actually holding it accountable to ordinary people.
And we know that law enforcement has a pattern of systemically depriving communities that are already marginalized: Black communities, Latinx communities, poor communities, Muslims, disabled communities. I mean, the list goes on.
So, basically, CNN is signaling that this is where they’re putting their weight.
JJ: Yeah. And you know, at that point, Josmar Trujillo was writing about how the NYC City Council was calling on the police department to be transparent about surveillance operations. That was something called the POST Act, and the police and the right-wing media came in shrieking, like this is going to be a “roadmap for terrorists” to how to attack us.
But the point is, that hysteria pulled the goalpost to the right. So now transparency—what surveillance operations are you doing—becomes the weirdest thing that you can call for. And ending that discriminatory surveillance and harassment is pushed off the page and off the table.
And I just wonder what your thoughts are about media and journalism, and what they could do to help, or could stop doing that hurts.

Sumayyah Waheed: “News networks are supposed to help us sort fact from fiction, not further destroy the line.”
SW: Right. I think that, again, going back to my point that news networks are supposed to help us sort fact from fiction, not further destroy the line, and specifically with the powerful actors, whether they’re police departments or elected officials, to utilize that truth-telling, the investigatory process, to hold those actors accountable.
Because that should be the role of the news, is finding the information that might not be obvious, accessing the records that should be public, because we live in a free and open society, supposedly, and enabling people to take that information and hold their elected or public officials accountable.
So simply ceding ground because there’s a loud, screaming, radical voice out there is definitely not the answer. And to further reiterate, you know, the AP, by reporting on this, won the Pulitzer Prize. So it’s not like there’s no reward for it besides, you know, a free and well-engaged society. We should be rewarding truth-telling and proper investigations by journalists.
But you know, this is a rightward shift at CNN under the new chairman, and it comes after the firing of Brian Stelter and John Harwood for criticizing Trump and Republicans who engage in election denials.
So the story is already being told by these moves, right? So it’s just really alarming and disturbing for anyone who values truth, who values our democracy—and particularly for the marginalized communities, who know that this type of gaslighting, this type of elevating law enforcement above any kind of reproach is going to continue to harm us.
JJ: And I wish I didn’t have to note that nothing about that program made anybody safer.
SW: Yes.
JJ: Because what we’re going to hear is, “OK, yeah, we’re harming some people’s civil liberties, but it’s all about safety.”
And so I wish we didn’t have to say it, but the thing is that that harm didn’t make anybody safer.

FAIR.org (9/14/22)
SW: Right, the entire massive surveillance apparatus did not lead to one investigatory lead.
And I’ll also point out: the federal appeals court that ruled for our clients also cited the Japanese internment as a bad example of being overly deferential to the executive branch, which law enforcement is part of, and not wanting to repeat that shameful history.
So one step towards repeating history is denying it. Another step is forgetting it. But active denial just accelerates that process. So it’s very unsettling, and CNN should really just reverse course, but I don’t know if that’s going to happen, so it’s pretty discouraging.
JJ: Well, we’re going to encourage listeners to encourage that to happen.
We’ve been speaking with Sumayyah Waheed, senior policy council at Muslim Advocates. You can find their work online at MuslimAdvocates.org. Thank you so much, Sumayyah Waheed, for joining us this week on CounterSpin.
SW: Thank you. Pleasure to be here.
The post John Miller ‘Chose to Lie About Something That’s Well-Documented’ appeared first on FAIR.
This post was originally published on FAIR.